Hi everyone, In this sixth and the final part of VIDM series, I will be discussing on multi-factor authentication using Radius.
To work on this specific use case, I have created a on-premises Radius server on CentOS and using Google Authenticator app to get OTP. This is only piece of work which took sometime to work as expected. In production scenario, you will get this deployed and managed by a specific professional team. Let’s get started with the configuration
- Login to VMware Identity Manager admin console and navigate to Identity & Access Management > Setup > Connectors.
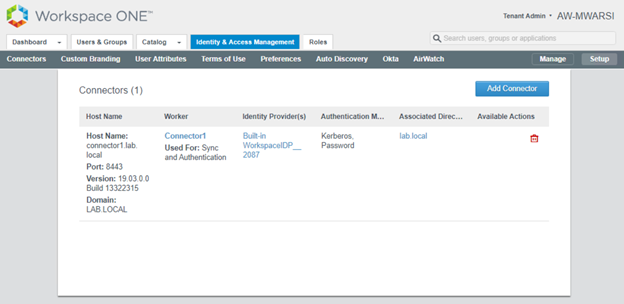
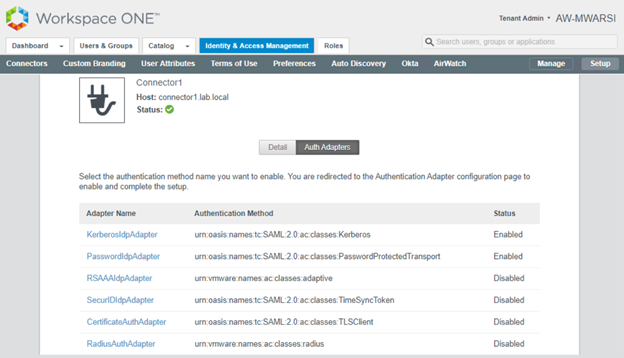
- Click on connector name under Worker (Connector1) and click on Auth Adapters and then click on RadiusAuthAdapter
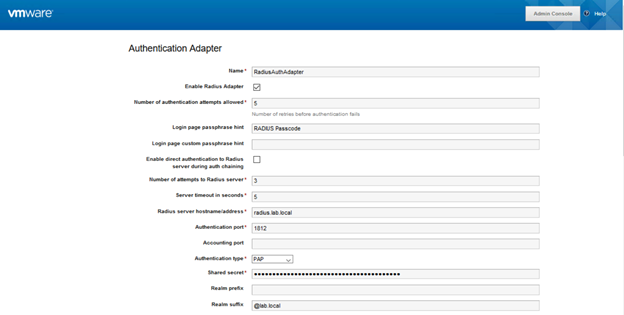
- A new Window will get open for Adapter configuration with SSO. Check Enable the adapter,
Enter Radius Server hostname/address
Select Authentication type as supported by Radius server
Enter Shared Secret which will be shared by Radius Team
Add Realm Suffix if you are using user name as logon in VIDM portal.
You can add two radius server, in my case I have only one. Click on Save
- Next, we need to enable Radius authentication in the IDP. Navigate to Identity & Access Management > Manage > Identity Providers
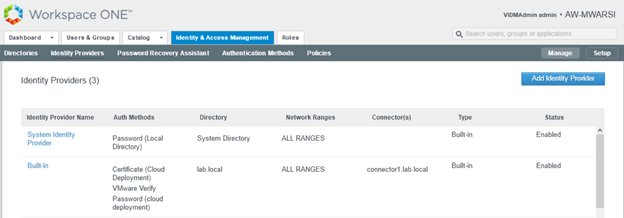
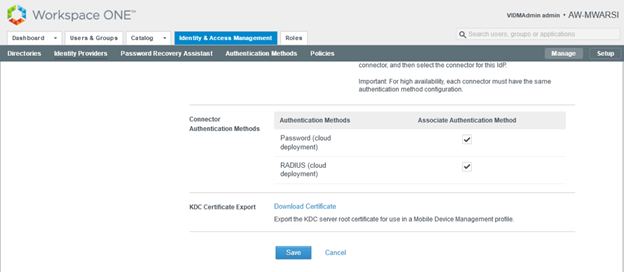
- Click on Built In Identity Provider and scroll down, you will see one more Connector Authentication method is available as Radius (Cloud deployment). Select it and click on Save
- Finally, we have to update the policy to use this authentication method. Navigate to Identity & Access Management> Manage> Polices. Click on Edit Default Policy> Configuration > Edit Policy Rule and select Radius (Cloud deployment)
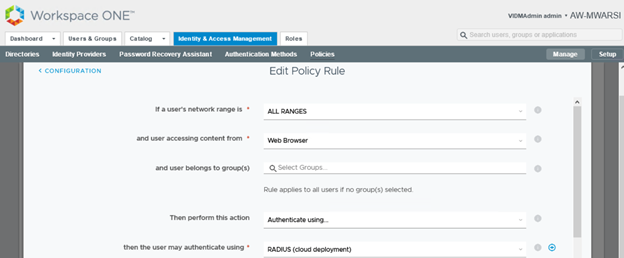
- Save the Rule and Finish edit Policy Wizard
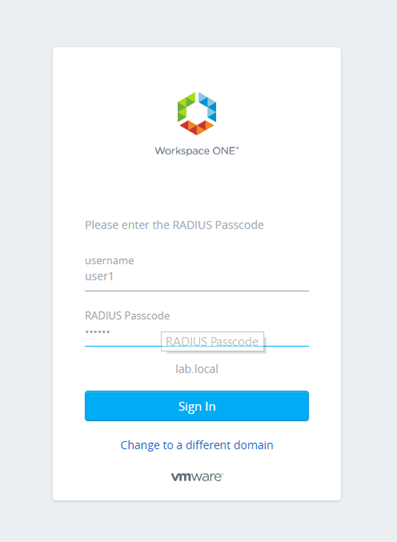
Login to end user machine. Launch IE/Chrome and access the VMware Identity Manager URL. Enter your Username and Radius passcode from Google Authenticator app and click on Sign in
Note: To get Radius Passcode for user, kindly follow this article
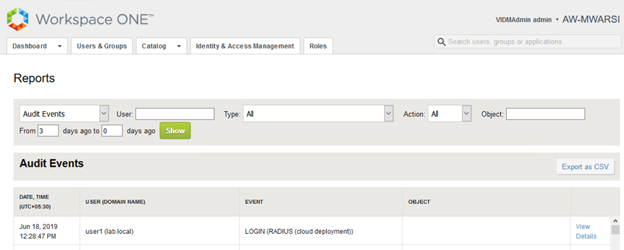
- Login to VMware Identity Manager admin console and navigate to Dashboard>Reports> Audit Events and filter Type with Login. It shows MFA id got created for user and MFA enrollment is done as well as User logged into portal with Radius (Cloud deployment).